Dynamics
|
Generational Dynamics |
| Forecasting America's Destiny ... and the World's | |
| HOME WEB LOG COUNTRY STUDIES COMMENT FORUM | |
| DOWNLOADS FOURTH TURNING ARCHIVE ABOUT | |
Google is repeating the mistakes that IBM made in helping the Nazis
by
John J. Xenakis
This morning's key headlines from GenerationalDynamics.com
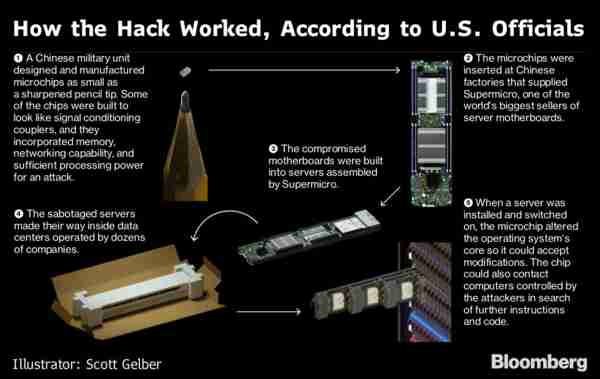 |
The announcement this week by Bloomberg News that an investigation has found that China is installing backdoor chips on server motherboards is making the public aware of a major security issue that will affect a wide variety of electronic products, from iPhones to televisions to automobile components.
The attack worked as follows:
Apple and Amazon initially denied they were victims of this attack, but apparently later confirmed that they were.
China's foreign ministry denied that they would ever do such a thing, but said that they were victims of such attacks themselves.
These revelations have exposed only a tiny part of the problem, which is being described as the "supply chain problem." These days, any electronic device contains chips and components from many sources, and those components themselves may be made up of chips from many sources. A complex electronic device might contain over 100 chips, sourced from different locations. If just one of those chips has been infected by China's military, then the entire device could be compromised. As soon as the device is turned on, then the malware chip "calls home" to the Chinese military, which then has access to the entire device, whether it's an iPhone or a helicopter. Bloomberg and Bloomberg and Krebs on Security and Mashable
For months, American intelligence agencies have been advising Americans not to do business with Chinese chip manufacturers Huawei Technologies Co. or ZTE Corp.
China goes out of its way to tempt Americans to buy their products, by offering a lot of features and setting very low prices. The Chinese undoubtedly lose money on these sales, but the sales support a national effort for China to control as many American electronic devices as possible, for future warfare.
As a Senior Software Development, I've developed embedded operating systems for chips, and I personally know how easy it would be for the Chinese to implement this policy. Huawei could develop a chipset that works fine during tests, but Huawei could install a "backdoor" into the chipset. When the chip receives, say, a secret 1024-bit code, then it will execute commands sent to it by China's military. Thus, the Chinese are then in control of any devices with Huawei or ZTE chips. This is not only doable, it's easy to do. The "backdoor" could not be detected until an attack had been launched, and then it would be too late. So there's never been any doubt in my mind that China COULD do this, and if China CAN do it, then they WILL do it, because they've engaged every part of the nation to prepare for war with the United States.
That's a different kind of situation than the one that's been revealed this week. In this week's case, the hacking was done not by "invisible" software, but by a visible but tiny piece of hardware.
SecurityWeek took a survey of reactions by security experts to the announcement of China's spy chips, and what was remarkable is that no one was the least surprised.
Sanjay Beri, CEO, Netskope, said: "Chinese cyber infiltration is nothing new, as proven by ongoing recent attacks from elite Chinese institutions diligently working to gain access to assets from the west."
Itzik Kotler, CTO and Co-Founder, SafeBreach, said: "Like many recent attacks, this is low-level, stealthy, and widespread. The combination of these three makes it especially frightening at first, and it certainly is rare to see such an attack in the wild."
Rick Moy, Chief Marketing Officer at Acalvio said: "While there�s a lot of denial about the attacks, it�s completely plausible that China did in fact seed certain hardware with these backdoor chips. One can imagine the liabilities that firms would rather not take on by admitting this kind of a breach. However, it is entirely within the capabilities and mission scope of nation state intel armies to infiltrate supply chains in this way."
Joseph Carson, chief security scientist at Thycotic said: "We are one step away from a major cyber conflict or retaliation that could result in serious implications. This could be one of the biggest hacks in history. What is clear is that it is a government behind this cyber espionage and I believe it is compromised employees with privileged access that are acting as malicious insiders selecting specific targets so the supply chain has been victim of being compromised."
Malcolm Harkins, Chief Security and Trust Officer, Cylance: Unfortunately the only surprising element about this attack is that it�s taken so long to be uncovered in a report." Security Week
In the late 1930s, Thomas Watson, the founder of IBM Corp. had to decide whether to sell Hollerith card tabulating equipment to the German Nazis, at a time when they were persecuting Jews and even dropping bombs on London. Nominally, the equipment was to be used to count things like cars and cows, but it was obvious that it could also be used to count Jews. Watson did business with the Nazis even during the war, and helped the Nazis with the Holocaust.
Now Google appears to be making the same mistake with China.
Google recently announced it would not help the Department of Defense with AI technology, even for purely defensive purposes. (Paragraph corrected, 13-Oct)
At the same time, Google announced a major new Google AI research center in China. �I believe AI and its benefits have no borders� said Dr. Fei-Fei Li, Chief Scientist at Google Cloud. Well that's a lie. Google's AI technology will only be used outside the United States border, and inside China's border.
China is preparing for war with the United States, and has developed numerous weapons systems with no other purpose than to attack American cities, bases and aircraft carriers. Google is willing to provide AI technology to China that can be used in these weapons to attack the United States, but refuses to allow the U.S. to use its AI technology to defend itself from China's weapons. That's verging on treason.
A separate issue is Google's Dragonfly project. Google is using AI technology to develop a search engine for the Chinese government that will automatically track Chinese citizens who make unapproved searches, and then report those individuals to the government. Vice President Mike Pence this week called on Google this week to stop development of Dragonfly, because it would "strengthen Communist Party censorship and compromise the privacy of Chinese customers."
China's persecution of the Uighurs and Tibetans in China is worse than the Nazi persecution of the Jews. Recent reports indicate that over a million Uighurs are imprisoned in reeducation camps. AI software provides facial recognition capabilities that permit China to track the movements of all Uighurs in Xinjiang province (or other Chinese citizens) for arrest or persecution.
My guess is that during the 1930s it was young German-Americans who promoted selling IBM technology to the Nazis. Today, with Google located in Silicon Valley, it's probably young Chinese who are promoting selling AI technology to the Chinese military, but opposing its sale to the U.S. military. These Chinese workers will certainly come to grief for this betrayal of America. Guardian (London, 29-Mar-2002) and Atlantic (April 2001) and Task and Purpose (19-Jun) and The Verge
Related Articles:
(Comments: For reader comments, questions and discussion, see the 6-Oct-18 World View --China's spy chip attacks shock the computer industry thread of the Generational Dynamics forum. Comments may be
posted anonymously.)
(6-Oct-2018)
Permanent Link
Receive daily World View columns by e-mail
Donate to Generational Dynamics via PayPal
Web Log Summary - 2018
Web Log Summary - 2017
Web Log Summary - 2016
Web Log Summary - 2015
Web Log Summary - 2014
Web Log Summary - 2013
Web Log Summary - 2012
Web Log Summary - 2011
Web Log Summary - 2010
Web Log Summary - 2009
Web Log Summary - 2008
Web Log Summary - 2007
Web Log Summary - 2006
Web Log Summary - 2005
Web Log Summary - 2004
Web Log - December, 2018
Web Log - November, 2018
Web Log - October, 2018
Web Log - September, 2018
Web Log - August, 2018
Web Log - July, 2018
Web Log - June, 2018
Web Log - May, 2018
Web Log - April, 2018
Web Log - March, 2018
Web Log - February, 2018
Web Log - January, 2018
Web Log - December, 2017
Web Log - November, 2017
Web Log - October, 2017
Web Log - September, 2017
Web Log - August, 2017
Web Log - July, 2017
Web Log - June, 2017
Web Log - May, 2017
Web Log - April, 2017
Web Log - March, 2017
Web Log - February, 2017
Web Log - January, 2017
Web Log - December, 2016
Web Log - November, 2016
Web Log - October, 2016
Web Log - September, 2016
Web Log - August, 2016
Web Log - July, 2016
Web Log - June, 2016
Web Log - May, 2016
Web Log - April, 2016
Web Log - March, 2016
Web Log - February, 2016
Web Log - January, 2016
Web Log - December, 2015
Web Log - November, 2015
Web Log - October, 2015
Web Log - September, 2015
Web Log - August, 2015
Web Log - July, 2015
Web Log - June, 2015
Web Log - May, 2015
Web Log - April, 2015
Web Log - March, 2015
Web Log - February, 2015
Web Log - January, 2015
Web Log - December, 2014
Web Log - November, 2014
Web Log - October, 2014
Web Log - September, 2014
Web Log - August, 2014
Web Log - July, 2014
Web Log - June, 2014
Web Log - May, 2014
Web Log - April, 2014
Web Log - March, 2014
Web Log - February, 2014
Web Log - January, 2014
Web Log - December, 2013
Web Log - November, 2013
Web Log - October, 2013
Web Log - September, 2013
Web Log - August, 2013
Web Log - July, 2013
Web Log - June, 2013
Web Log - May, 2013
Web Log - April, 2013
Web Log - March, 2013
Web Log - February, 2013
Web Log - January, 2013
Web Log - December, 2012
Web Log - November, 2012
Web Log - October, 2012
Web Log - September, 2012
Web Log - August, 2012
Web Log - July, 2012
Web Log - June, 2012
Web Log - May, 2012
Web Log - April, 2012
Web Log - March, 2012
Web Log - February, 2012
Web Log - January, 2012
Web Log - December, 2011
Web Log - November, 2011
Web Log - October, 2011
Web Log - September, 2011
Web Log - August, 2011
Web Log - July, 2011
Web Log - June, 2011
Web Log - May, 2011
Web Log - April, 2011
Web Log - March, 2011
Web Log - February, 2011
Web Log - January, 2011
Web Log - December, 2010
Web Log - November, 2010
Web Log - October, 2010
Web Log - September, 2010
Web Log - August, 2010
Web Log - July, 2010
Web Log - June, 2010
Web Log - May, 2010
Web Log - April, 2010
Web Log - March, 2010
Web Log - February, 2010
Web Log - January, 2010
Web Log - December, 2009
Web Log - November, 2009
Web Log - October, 2009
Web Log - September, 2009
Web Log - August, 2009
Web Log - July, 2009
Web Log - June, 2009
Web Log - May, 2009
Web Log - April, 2009
Web Log - March, 2009
Web Log - February, 2009
Web Log - January, 2009
Web Log - December, 2008
Web Log - November, 2008
Web Log - October, 2008
Web Log - September, 2008
Web Log - August, 2008
Web Log - July, 2008
Web Log - June, 2008
Web Log - May, 2008
Web Log - April, 2008
Web Log - March, 2008
Web Log - February, 2008
Web Log - January, 2008
Web Log - December, 2007
Web Log - November, 2007
Web Log - October, 2007
Web Log - September, 2007
Web Log - August, 2007
Web Log - July, 2007
Web Log - June, 2007
Web Log - May, 2007
Web Log - April, 2007
Web Log - March, 2007
Web Log - February, 2007
Web Log - January, 2007
Web Log - December, 2006
Web Log - November, 2006
Web Log - October, 2006
Web Log - September, 2006
Web Log - August, 2006
Web Log - July, 2006
Web Log - June, 2006
Web Log - May, 2006
Web Log - April, 2006
Web Log - March, 2006
Web Log - February, 2006
Web Log - January, 2006
Web Log - December, 2005
Web Log - November, 2005
Web Log - October, 2005
Web Log - September, 2005
Web Log - August, 2005
Web Log - July, 2005
Web Log - June, 2005
Web Log - May, 2005
Web Log - April, 2005
Web Log - March, 2005
Web Log - February, 2005
Web Log - January, 2005
Web Log - December, 2004
Web Log - November, 2004
Web Log - October, 2004
Web Log - September, 2004
Web Log - August, 2004
Web Log - July, 2004
Web Log - June, 2004